Enterprise-Grade Security
Multi-Layer Encryption
Defense-in-depth encryption strategy protects data at every layer of the application stack — from user access to network transport to message integrity.
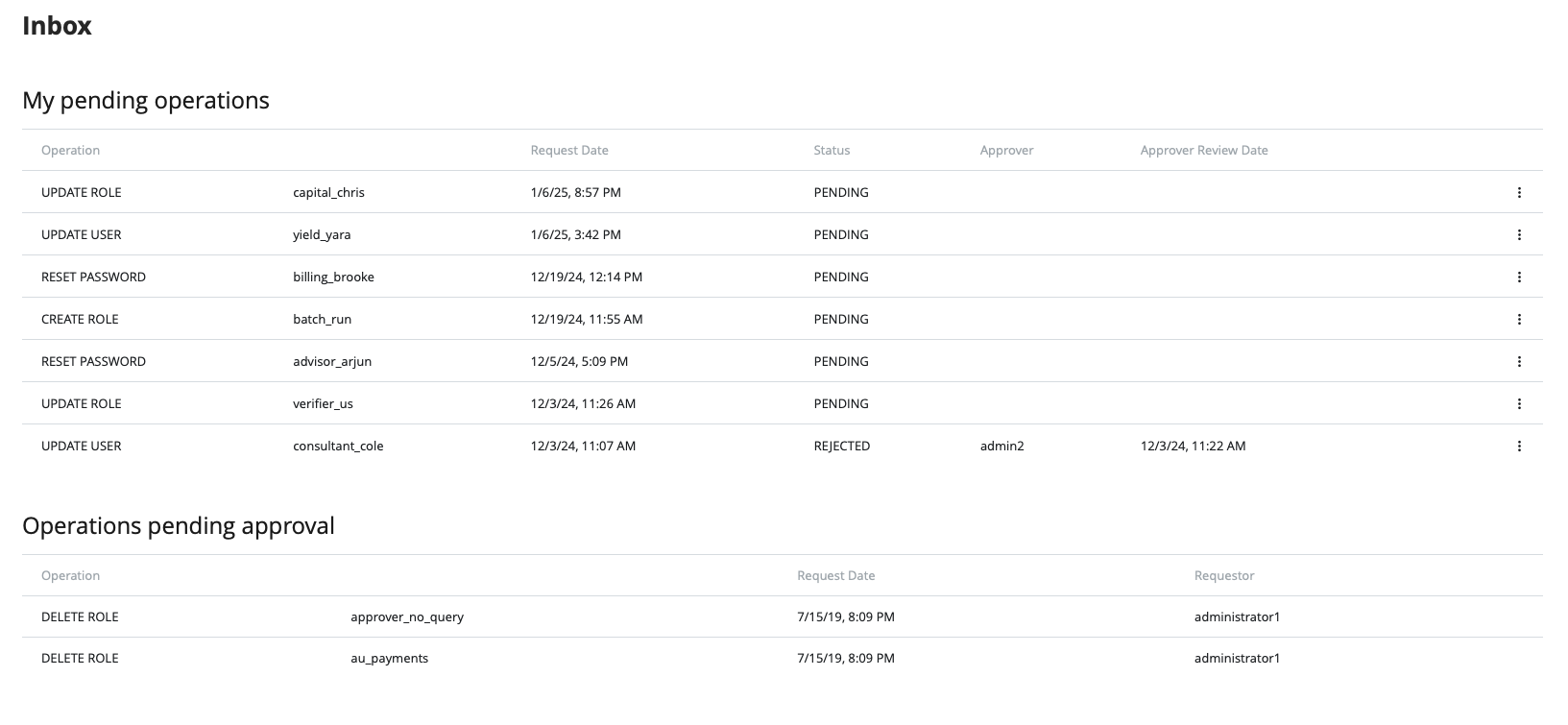
4-Eyes Principle
Built-in support for verification and authorization workflows across both business messages and administrative operations.
Data Segregation
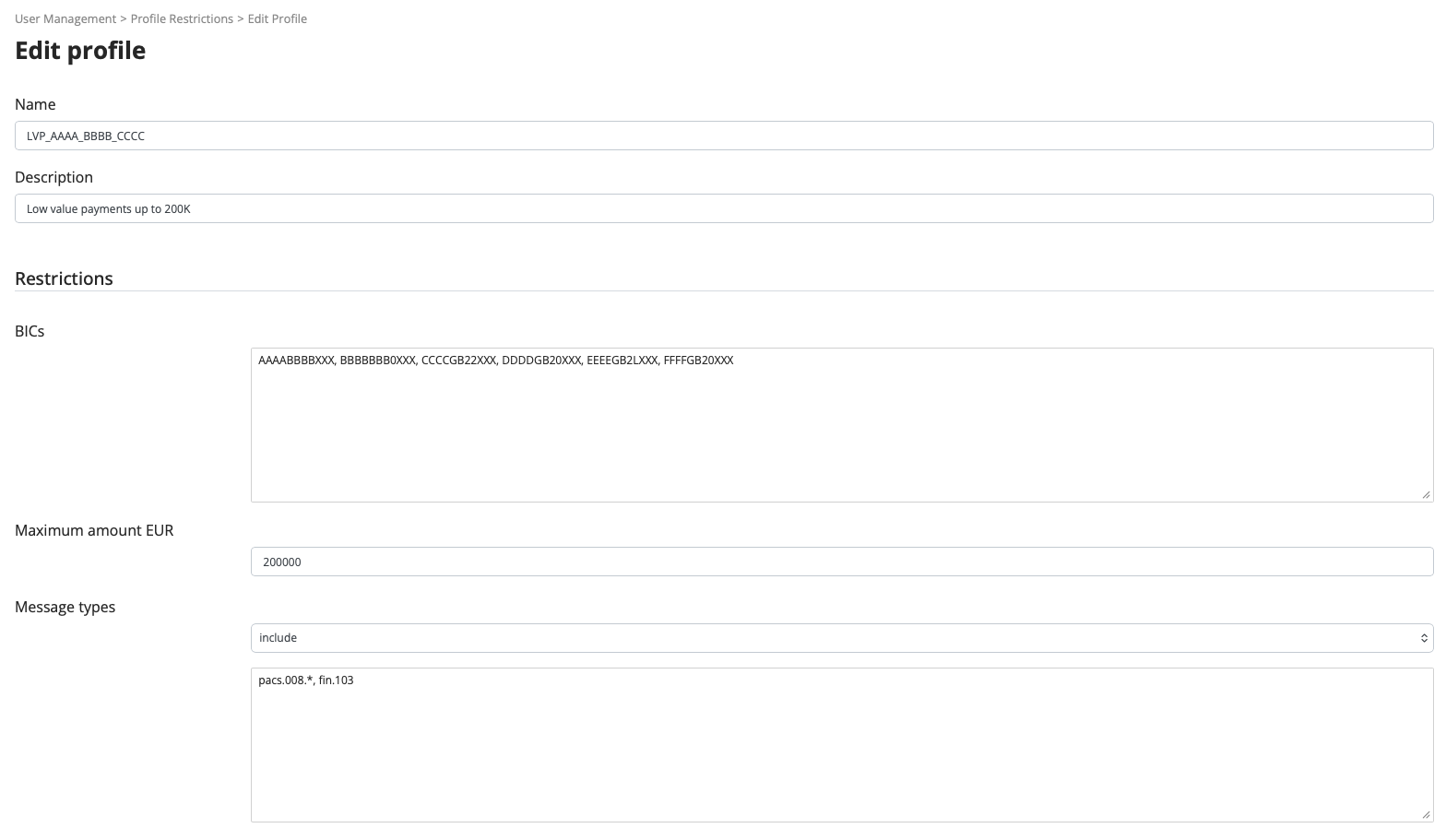
User profiles enable data segregation for fine-grained protection. Different departments or entities can be isolated within the same platform instance.
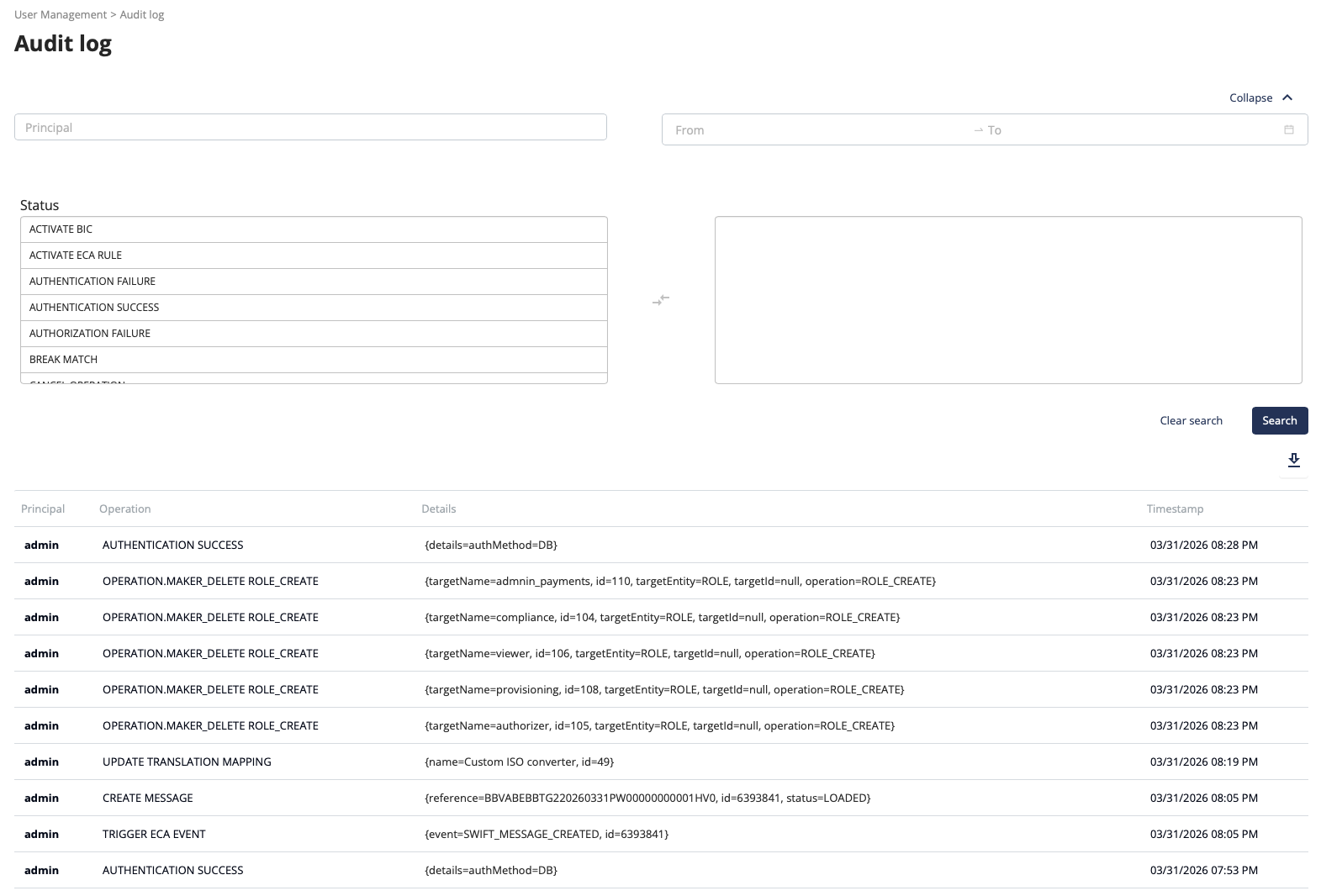
Audit Logging & Compliance
Comprehensive audit trail preserving session information, audit records, and detailed message processing traces.
REST API Security
JWT token-based authentication reduces credential exposure over the network. Token-based approach enables secure system-to-system integration with stateless authentication. Role-based access control extends to REST API resources with same granular permissions as the UI.
Content Security Policy
CSP headers prevent XSS and code injection attacks. Configurable frame-ancestors control iframe embedding. Defense-in-depth security approach following modern web application security standards.
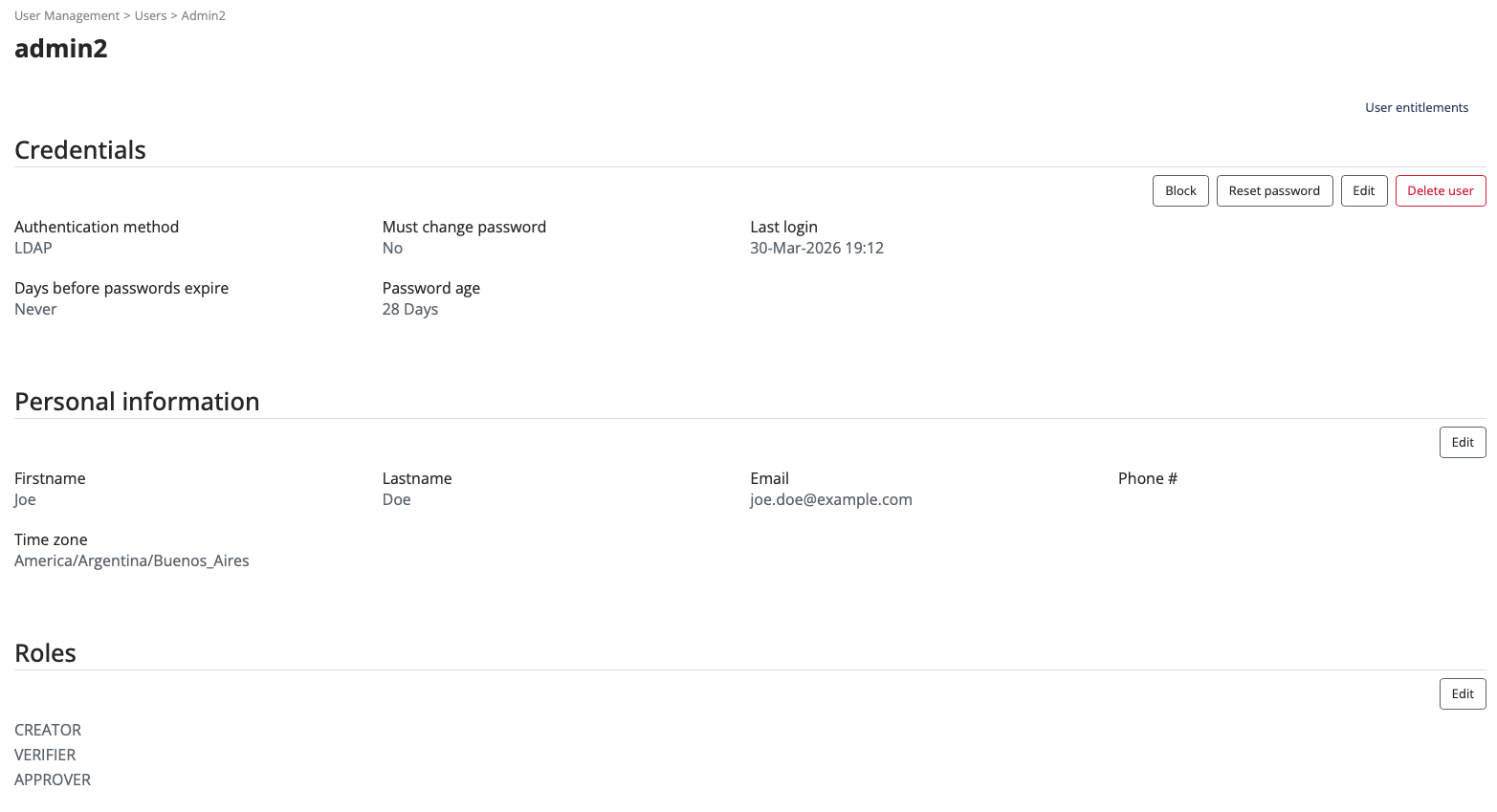
Password Security Controls
Configurable password complexity (length, uppercase, lowercase, digits, special characters). Password history validation prevents reuse. Automatic account lockout after failed login attempts. Passwords hashed — never stored in plain text.
Session Management
Multi-device concurrent sessions with per-browser isolation. Configurable automatic timeout (15 minutes default). Complete login history with timestamps and IP addresses for all successful and failed attempts.
User & Access Management
Role-based access control with granular permissions and data segregation by organizational units for multi-tenant environments.
Your Infrastructure, Your Data
Deploy on-premises or in your private cloud with full control over data residency and sovereignty.
Network-Agnostic
Works with SWIFT and proprietary networks — no vendor lock-in on connectivity.
Faster Deployment
Faster deployment than typical enterprise solutions with lower operational overhead.
Perpetual Licensing
Own the software — not subscription-based. Fully customizable to your workflows.